
This question comes from a user whose site recently got attacked with malware. Before reading the answer, please do read How to remove malware from a hacked WordPress site.
Depending on what needs restoration, this question can have multiple answers:
However considering that you have removed all your WordPress installation files, you’ll need to restore the files from a known-good backup.
Table of Contents
Database is Intact; WordPress Files are Infected
In an ideal situation this means that your database remains intact. This includes your settings, posts, pages etc.
Instead of reinstalling WordPress you’ll need to extract the files from the WordPress core package.
- Make sure that
wp-config.phpin the root of your installation has the correct settings. - Download the core files from https://downloads.wordpress.org/release/wordpress-5.8.3-no-content.zip (replace the version with the correct one). Extract and overwrite the files on your WordPress install.
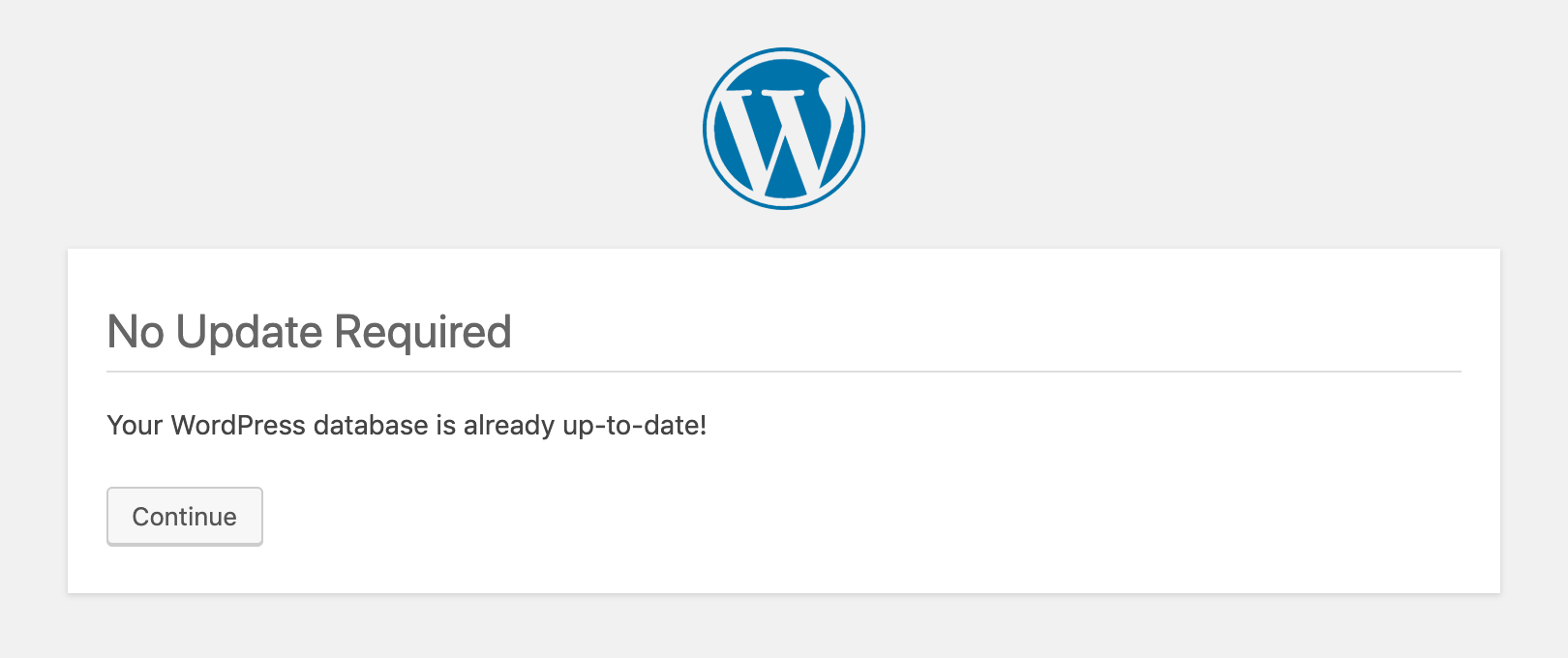
- Point your browser to <yourwebsiteurl>/wp-admin/upgrade.php. This will make sure that a database upgrade runs.
- Log into the website admin area.
- Purge the cache.
- Verify that you have the required theme and plugins active.
- Visit the permalinks settings once. This will create a .htaccess file or verify and update it if one already exists.
- Visit the front-end of the website and verify that all is well.
- Log into Google Search Console and head over to URL Inspection Tool.
- Enter the URL of the homepage or select any URL of your website.
- Click on “Test Live URL”.
- Click on “View Tested Page”.
- Very the site in “Screenshot” and “More Info” tabs.
If you have access to WP CLI, you can also reinstall WordPress with some very easy to follow steps. This is quicker than manual extraction and uploading.
Step-by-Step guide to efficiently reinstalling infected WordPress Core using WP CLI
Database is Infected; WordPress Files are Intact
Fixing an infected database is slightly more involved and you’ll certainly need access to WP CLI.
- Run a malware scan with Malcure Malware Scanner.
- The scan will outline the infected database records.
- Use PHPMyAdmin to inspect the infected records and identify the malware / malicious code.
- Find and replace: The WordPress database contains serialized data so bare-hand find and replace will break the data integrity. Use the WP CLI to do a search and replace.
- Execute the following command via WP CLI replacing the malicious code with the one that you detected on your WordPress install. In case of several types of malicious code you’ll need to run it multiple times.
wp search-replace 'malicious code' '' --all-tables --dry-run --report-changed-only --precise --regex --regex-delimiter='/'
If there is a large database dump, here is what you will need to do:
Different Use Cases and Scenarios for Malware Cleanup
There are different types of malware attacks, here are some of the different use cases of malware attacks with respective steps to cleaning the infection and restoring the site:
- How to clean-up a website blocked by the web-host?
- Removing JavaScript Redirect Malware from WordPress
- How to Detect & Remove Cryptojacking Malware
- Fixing WordPress Spam Injection — Hybrid File + Database Malware Infection
- What is the WordPress Pharma Hack & How to fix it
- How to Clean-Up Vuln.php Recurring Malware Infection
Run Another Malware Scan to Ensure Clean Site
Whatever the case, be it database infection, files infection or database and file infections both, after cleaning the infection it’s time to run another malware scan to ensure there are no remaining traces of the malicious code / malware. It is important to clear the cache before running the second scan to avoid cached versions of infected files.
Ensure that SERPS are clean
There are use cases of SEO spam and website redirects specifically via search engine results. That is why it is important to search for your site in search-engines. If you see weird results then it’s time to ask the search-engines to re-index your website or specific URLs. Also check your Google Search Console account for any malware warnings, etc.
That’s pretty much it! If you need help with this part of the process checkout our Malware Removal Service.